

February 15, 2024
December 13th, 2024
In this era of digitalization, mobile apps play a huge role in our day-to-day lives. We use mobile apps to fulfill our day-to-day needs. You can easily do secure transactions, buy groceries, and food, and shop online with just a few clicks. All app service companies do mobile app security testing to protect user data.
From 2024 to 2029, the amount of people using smartphones worldwide is predicted to rise by 1.5 billion, a 30.6% increase. By 2029, it’s projected to hit a record high of 6.4 billion users, with consistent growth observed over the past years. (Source – Statista)
Hence, the percentage of people using mobile apps in their daily lives has also increased. Strong mobile security is the top priority as smartphone and app use will keep growing.
As we rely more on apps, it’s crucial to prioritize mobile app security testing. Smartphone and app usage will continue to grow, making it even more important.
Today we will discuss everything you need to know about mobile app security. We will discuss the importance of app testing techniques, mobile app security tools, and best practices. Additionally, we will explore real-life examples, laws to follow, and possible challenges.
These days, verifying the security of mobile apps is crucial. Your data is the most important thing. Security lapses can serious financial and brand harm to companies in addition to compromising private user information. Given the current state of threats, it is imperative to invest in strong security measures.
Let’s talk about a few key elements and the importance of mobile application security testing.
Data Protection: Mobile apps handle important user data, such as personal info, finances, and app login details. These are the crucial details that no one prefers to share with anyone. Your security system must prevent the users from facing issues like identity theft, and financial fraud.
Privacy Preservation: When utilizing mobile apps, users anticipate that their privacy will be upheld. App Security techniques like permission management, data storage, and encryption protect user privacy from misuse or compromise.
Trust and Reputation: A security breach has the potential to seriously harm an app’s standing and erode users’ confidence. App developers must prioritize app security to demonstrate their commitment to protecting user information. Users must be able to interact in a secure setting.
Regulatory Compliance: Strict rules and regulations are there from Government bodies related to data protection and privacy. For example, GDPR in Europe and CCPA in California. Apart from his HIPAA, PCI DSS standard cybersecurity policies are also there. You must take care of these regulations to avoid legal repercussions and financial penalties.
Financial Loss Prevention: Security breaches can result in financial losses. Costs associated with data breaches include legal fees, compensation to affected users, and damage to brand reputation. The strong security measures are well worth the expense because of all these drawbacks.
Intellectual Property Protection: Mobile apps can contain valuable intellectual property like trade secrets, copyrighted content, and proprietary algorithms. Making sure the software is secure stops theft of intellectual property and unwanted access.
Continuity of Service: Security issues can make an app stop working, causing service interruptions and upsetting users. Developers may provide a smooth user experience and maintain service continuity by taking proactive measures to mitigate security concerns.
Mitigation of Cyber Threats: Mobile apps can face cyber threats like malware, phishing, and man-in-the-middle attacks. You need to put in place strong security measures in order to stop these threats.
Numerous dangers associated with insecure mobile apps can affect both individuals and enterprises. One of these concerns is the possibility of data breaches.
Sensitive user data, including financial and sensitive information, may become public, increasing the risk of identity theft and privacy violations.
Additionally, malware infections can occur in insecure programs. They increase the possibility of device compromise and illegal access to user data. Insecure apps may be the source of ransomware attacks or fraudulent transactions that result in financial losses.
Additionally, security events expose firms to legal liabilities and reputational harm, which could lead to a decline in user trust and bad press.
Another issue is intellectual property theft because insecure apps can be reverse-engineered, which makes it possible to steal copyrighted material and proprietary algorithms.
Insecure apps that reveal location data or permit cyberbullying and predatory behavior can pose a risk to user safety. It is essential to address these vulnerabilities.
Testing mobile apps involves various methods such as –
Manual testing involves human testers executing test cases. Automated testing uses software tools for faster and more efficient testing. Usability testing focuses on the user interface and experience, while performance testing assesses responsiveness and stability.
Security testing identifies vulnerabilities to protect user data. Thorough testing ensures early issue identification, meets user expectations, and safeguards user data at the same time.
For several reasons, mobile apps must undergo comprehensive testing. It lessens the possibility threat, expensive corrections and rework by helping in the early identification of errors. It also makes sure that the app performs, functions, and satisfies user expectations, which increases user retention and happiness.
Security testing also aids in protecting user privacy and data from potential security breaches and problems with regulatory compliance. To make good mobile apps, you need to test them well to ensure they are reliable, secure, and meet customer expectations.
When it comes to developing mobile apps, security must always come first. Important resources for testing mobile security protect our virtual environment by finding ways to make our apps stronger. Mobile app security testing tools help in ensuring the accuracy of the security tool provided in the app.
Let us examine this collection of digital defenses one by one which are important for mobile application security testing.
Consider these instruments as watchful gatekeepers that examine each line of code with a critical eye. Veracode, Checkmarx, and Fortify are top companies that carefully examine code and binaries to find security risks. In their effort to maintain security standards, they look for and fix everything from buffer overflows to injection vulnerabilities.
These are the dynamic investigators of the digital realm, interacting in real-time with mobile applications to reveal hidden dangers. Use tools like OWASP ZAP, Burp Suite, and Wireshark to find insecure data transfers, weak session handling, and problematic input checking. By simulating actual situations, they make sure that our apps can withstand hardship.
Imagine these as fearless explorers, spelunking deep into our application’s infrastructure to find weaknesses. Metasploit, Nessus, and Nmap work together to find weaknesses like SQL injections, cross-site scripting, and unsafe server setups. They offer priceless insights that help us strengthen our defenses against possible dangers.
These programs look out for our electronic gadgets, making sure they’re secure and safe inside company walls. MDM solutions protect against unauthorized access and data breaches with encryption, wiping, and app whitelisting. It is one of the top mobile app security testing tools for mobile app security.
Think of these instruments as watchful guardians stationed at the entrances to the largest app shops. Google Play Protect and Apple App Store Review Guidelines check mobile apps for security before they are released online. They make sure the apps follow strict security standards.
At SPEC INDIA, we pride ourselves on our commitment to delivering secure and reliable software solutions to our clients.
Our Security Software Development Life Cycle (SSDLC) is a comprehensive process that integrates security practices at every stage of the software development journey.
Here is a brief of the step which we follow while developing a mobile app.
At SPEC INDIA, begins with meticulous requirement analysis. We identify and prioritize security needs based on project scope and objectives. We assess potential security risks and determine security goals for the software to lay a solid foundation.
In the second phase, our team carefully adds security measures to the software architecture while developing it. Security measures like access controls, encryption, and authentication are created and used to meet security needs.
Moving forward to the development phase, our skilled developers bring the design to life by implementing security features and controls according to the design specifications. They adhere to secure coding practices and guidelines to minimize vulnerabilities. Also, they ensure that the software is resistant to common security threats.
Once development is complete, we enter the testing phase, where rigorous security testing takes place. we identify and address vulnerabilities and weaknesses in the software to ensure its security posture. We do it through various techniques like static code analysis, dynamic application security testing (DAST), and penetration testing.
Upon successful testing, we move to the deployment phase, where the software is deployed to production environments. Here, we apply security configurations and implement security controls to shield the software from potential attacks and breaches.
Throughout the maintenance phase, we remain vigilant. We continuously monitor and maintain the software to address newly discovered security vulnerabilities and apply security patches and updates. We also ensure that security controls remain effective over time.
Finally, we conduct periodic reviews and updates to evaluate the effectiveness of security measures. We identify areas for improvement, and incorporate lessons learned into future iterations of the SSDLC process.
By following this comprehensive approach, SPEC INDIA helps organizations proactively address security concerns throughout the software development process. It reduces the risk of security incidents and ensure that software is secure, resilient, and compliant with regulatory requirements.
In the current digital environment, managing mobile app security is crucial to protecting user data and keeping confidence.
Observe the following recommended practices:
A sobering reminder of the importance of robust security mechanisms in the digital age is provided by real-world examples of security incidents utilizing mobile apps. Here are a few significant incidents:
In 2018, millions of Facebook users’ personal information was collected by Cambridge Analytica without their knowledge or permission. This Cambridge Analytica Data Scandal made clear the dangers of integrating third-party apps.
In 2016, 57 million users’ and drivers’ personal information was compromised by an Uber data leak. The hacker who took credit for the attack revealed to The New York Times that he had texted an Uber employee under the guise of a company information technology specialist. He deceived an employee through social engineering to obtain a password. The hackers then utilized this password to gain access to Uber’s systems.
Over the years, numerous security flaws and attacks have been used against WhatsApp. These vulnerabilities, which demonstrate the continuous difficulties in safeguarding communication platforms, have varied from encryption problems to remote code execution vulnerabilities. WhatsApp’s Massive Security Flaw in 2019 Reminded Us the Limits of Consumer Encryption Apps.
The well-known social media app TikTok has come under fire for its data privacy policies. They collected the browser history and location data of users. These concerns have raised questions about the app’s compliance with privacy regulations. Also, its commitment to users’ privacy was raised.
Mobile app security testing is a critical aspect of the development process, aimed at identifying and mitigating potential security risks and vulnerabilities within mobile applications.
With the increasing reliance on mobile devices for various tasks, ensuring the security of mobile apps has become more important than ever.
Effective security testing helps protect user data, prevent unauthorized access, and maintain the trust of users. However, this process comes with its own set of challenges, including –
A comprehensive strategy for mobile security testing is needed to overcome these obstacles. This approach should include comprehensive testing methodologies, specific tools, and skills.
Apart from this ongoing learning adaptation, and collaboration between developers, testers, and security specialists are also needed. By proactively addressing these challenges, developers can enhance the security of their mobile apps and protect users from potential threats and vulnerabilities.
Safeguarding mobile apps is crucial for protecting user data, maintaining trust, and complying with legal regulations.
Developers can ensure the security and integrity of their mobile apps in an ever-evolving threat landscape.
By employing robust mobile security testing methods, leveraging essential tools, adhering to best practices, and learning from real-life examples, they can ensure it. Additionally, complying with regulations and addressing challenges are essential components of maintaining app security.
Contact us now and let our team of professionals provide a comprehensive end-to-end software testing strategy.
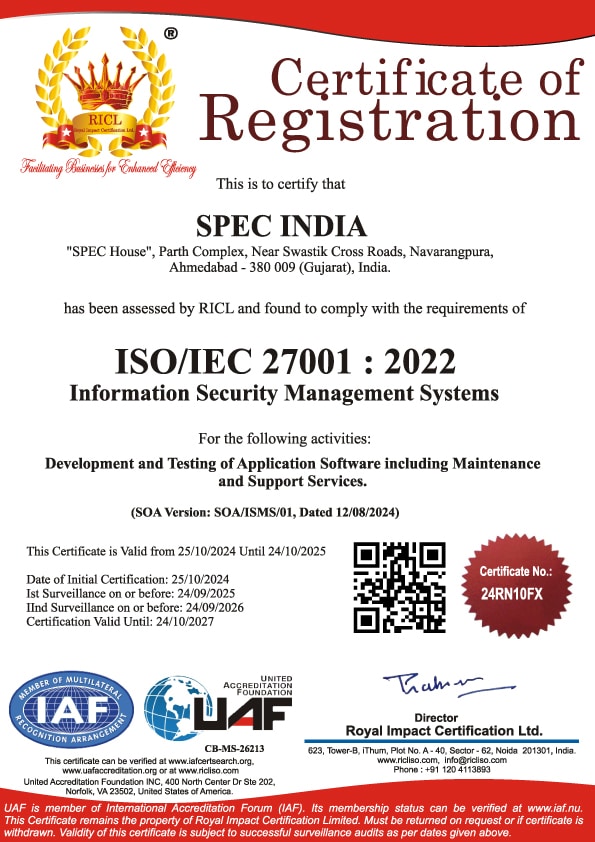
SPEC INDIA is your trusted partner for AI-driven software solutions, with proven expertise in digital transformation and innovative technology services. We deliver secure, reliable, and high-quality IT solutions to clients worldwide. As an ISO/IEC 27001:2022 certified company, we follow the highest standards for data security and quality. Our team applies proven project management methods, flexible engagement models, and modern infrastructure to deliver outstanding results. With skilled professionals and years of experience, we turn ideas into impactful solutions that drive business growth.
SPEC House, Parth Complex, Near Swastik Cross Roads, Navarangpura, Ahmedabad 380009, INDIA.
This website uses cookies to ensure you get the best experience on our website. Read Spec India’s Privacy Policy