

Access modifiers in Java are an essential aspect of the language that controls the visibility and accessibility of classes, methods, and variables. They are the guardians of encapsulation and play a crucial role in designing maintainable and secure software. In this comprehensive guide, we will explore the world of access modifiers in Java, understand their types, and learn how to use them effectively in your programming journey.
Java provides four main access modifiers, each with its distinct purpose and scope:
The most permissive of access modifiers, public members are accessible from anywhere. They are often used for classes, methods, or fields intended to be part of the public API. Public members create a contract with the outside world, and their behavior should be consistent over time.
Private members are the most restrictive. They are accessible only within the same class. This level of control is crucial for encapsulation, allowing you to hide the internal implementation details of a class from external interference.
Protected members are accessible within the same class, by subclasses, and by classes in the same package. They strike a balance between accessibility and encapsulation, making them useful for designing extensible classes.
When no access modifier is specified, the default modifier is applied. Members with the default modifier are accessible only within the same package, ensuring that classes within the package can collaborate effectively.
To make the most of access modifiers, consider these best practices:
Let’s explore practical examples of how to use these access modifiers effectively:
Public access is suitable for methods that provide a public API, such as getters and setters, as well as classes and interfaces meant to be widely used. It’s the gateway to your class, offering a clear and stable contract.
Use private access for helper methods or internal variables. Private members are crucial for maintaining encapsulation by hiding implementation details and preventing external interference.
Protected members are useful for methods or fields that should be accessible to subclasses and other classes in the same package. This access level allows for controlled extensibility and collaboration.
The default access modifier is ideal when you want members to be accessible only within the same package. It provides a balance between encapsulation and usability, allowing related classes to cooperate effectively.
Understanding and using access modifiers offer several benefits:
By controlling the visibility of your code, access modifiers protect it from unintended access and tampering. Private members, in particular, safeguard sensitive data from unauthorized access.
Access modifiers play a pivotal role in encapsulation, a fundamental concept in object-oriented programming. Encapsulation allows you to hide the internal implementation details of a class, making it easier to change or extend the class without affecting the outside world.
By enforcing clear boundaries in your code, access modifiers make it easier to manage, maintain, and extend your classes. You can confidently refactor or enhance your code without worrying about unintended side effects.
Now, let’s explore real-world scenarios where access modifiers come into play:
When designing public APIs for libraries and frameworks, you’ll use the public access modifier extensively. Classes and methods that are part of the public API should be marked as public to make them accessible to external developers. This ensures that the API is easily utilized by others.
In the implementation of a class, private access modifiers are often used for data members that should remain hidden from the outside world. For example, in a Personal class, sensitive data like a social security number should be private to prevent unauthorized access.
When creating a class intended to be subclassed, using protected access modifiers allows specific methods or fields to be accessible to subclasses. This controlled extensibility is valuable for maintaining the integrity of the base class.
The default access modifier is suitable for classes or methods that should be accessible only within the same package. This access level fosters collaboration between closely related classes while still providing a level of encapsulation.
While access modifiers offer numerous benefits, they come with their set of challenges and potential pitfalls:
Excessive use of the public access modifier can lead to overly complex and tightly coupled code. It’s important to strike a balance between providing access and maintaining encapsulation. Overexposure to implementation details can make it challenging to evolve and refactor the code.
While encapsulation is essential, overusing the private access modifier can make a class difficult to extend or modify. It’s crucial to strike a balance and consider the needs of the class’s design. For example, making all methods and fields private can hinder subclassing and extensibility.
Default access within a package can lead to tight coupling between classes in the same package. This can make it harder to change or refactor the code, as modifications to one class can have unintended consequences on others within the same package.
Access modifiers in Java are powerful tools for maintaining a secure and organized codebase. By understanding and using them effectively, you can strike the right balance between accessibility and encapsulation, ensuring your Java programs are robust and maintainable.
Whether you’re a novice or an experienced Java developer, mastering access modifiers is essential to creating efficient and maintainable code. These modifiers offer the control and flexibility you need to design classes and systems that are secure, extensible, and adaptable to changing requirements.
As you continue your programming journey, keep access modifiers in your toolkit and use them wisely. They are the guardians of your code’s integrity and the key to building software that stands the test of time.
With this extensive guide, you have a comprehensive understanding of access modifiers in Java and how to apply them effectively in your programming endeavors. Whether you’re building small applications or large-scale systems, access modifiers are your allies in the quest for secure, maintainable, and extensible code.
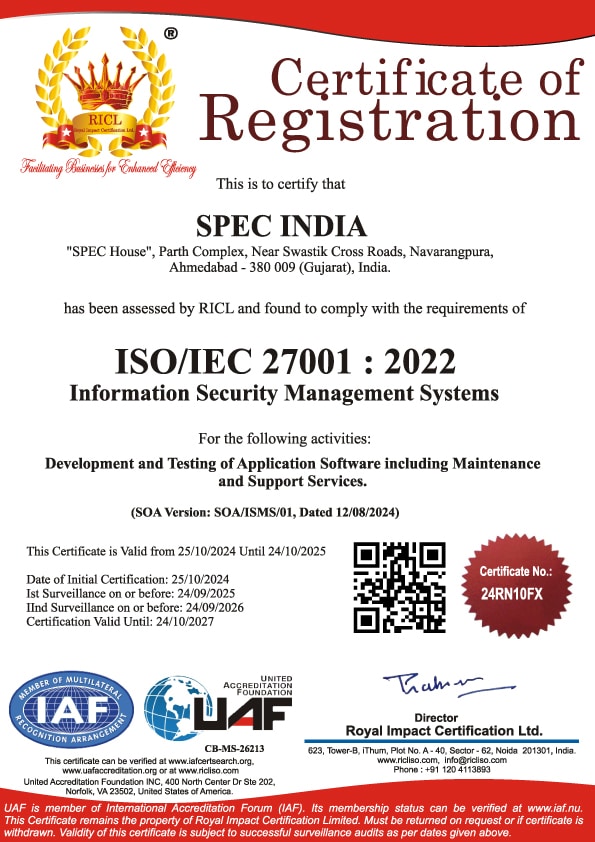
SPEC INDIA is your trusted partner for AI-driven software solutions, with proven expertise in digital transformation and innovative technology services. We deliver secure, reliable, and high-quality IT solutions to clients worldwide. As an ISO/IEC 27001:2022 certified company, we follow the highest standards for data security and quality. Our team applies proven project management methods, flexible engagement models, and modern infrastructure to deliver outstanding results. With skilled professionals and years of experience, we turn ideas into impactful solutions that drive business growth.
SPEC House, Parth Complex, Near Swastik Cross Roads, Navarangpura, Ahmedabad 380009, INDIA.
This website uses cookies to ensure you get the best experience on our website. Read Spec India’s Privacy Policy